DORA Metrics for Fintech: Proving Process Maturity to Regulators
Regulation is not the enemy of speed — lack of measurement is. The 2023 State of DevOps Report shows that top-quartile financial services organizations deploy daily while maintaining stricter change control than their slower peers. When an auditor asks "how do you ensure your deployment process is controlled and reliable?" you need a better answer than "we have code review." DORA metrics give you that answer — with quantitative evidence that auditors and risk committees can actually verify.
{/* truncate */}
The Regulatory Landscape for Fintech Delivery
Fintech companies operate under a growing web of regulations that directly affect how software is built and deployed. The key regulations and frameworks in 2026:
EU Digital Operational Resilience Act (DORA Regulation)
Yes, "DORA" appears twice in fintech — the DevOps Research and Assessment metrics, and the EU's Digital Operational Resilience Act (Regulation (EU) 2022/2554). This is not a coincidence in naming, but the two are distinct. The EU regulation took full effect in January 2025 and applies to:
- Banks and credit institutions
- Payment service providers
- Electronic money institutions
- Investment firms
- Insurance companies
- ICT third-party service providers
The regulation requires financial entities to maintain and test their ICT risk management frameworks, including software delivery and change management processes. Article 9 specifically requires "ICT change management" controls, including documentation, testing, and rollback capabilities.
PCI DSS 4.0
The Payment Card Industry Data Security Standard (version 4.0, effective March 2025) includes requirements for:
- Change control processes (Requirement 6.5)
- Documented change management procedures
- Testing of changes before deployment
- Rollback procedures
SOC 2 Type II
Not a regulation but effectively required for B2B fintech. SOC 2 audits evaluate:
- Change management controls
- System monitoring and incident response
- Risk assessment processes
Country-Specific Regulations
- UK: FCA requirements for operational resilience
- US: OCC guidance on third-party risk management, FFIEC IT Examination Handbook
- Russia/CIS: Central Bank regulations on information security for financial organizations (242-P, 683-P), with similar frameworks emerging across CIS jurisdictions
How DORA Metrics Map to Regulatory Requirements
Here's the key insight: DORA metrics provide quantitative evidence for controls that auditors typically verify through documentation review. Instead of showing auditors a 50-page change management policy that may or may not reflect reality, you show them live data.
Deployment Frequency → Change Management Control
| Regulatory Requirement | What Auditors Want to See | How DORA Data Helps |
|---|---|---|
| Changes are controlled and documented | Evidence that changes go through a defined process | Deployment Frequency data shows every production deployment, with timestamps, commit SHAs, and who triggered it |
| Changes are authorized | Approval before production deployment | MR approval data shows who reviewed and approved each change |
| No unauthorized changes | All production changes are tracked | Automated deployment tracking catches every change, including hotfixes |
What to show auditors: "In Q1 2026, we made 247 production deployments. 100% went through our CI/CD pipeline with mandatory code review. Here's the log."
Lead Time for Changes → Process Efficiency Evidence
| Regulatory Requirement | What Auditors Want to See | How DORA Data Helps |
|---|---|---|
| Efficient change process | Changes don't sit in queue for weeks | Lead Time data shows median time from commit to production |
| Separation of duties | Different people write, review, and deploy code | Lead Time stages show different participants at each stage |
| Review before deployment | All changes are reviewed | Pickup Time and Review Time show every change was reviewed |
What to show auditors: "Our median Lead Time is 3.2 days. Every change spends time in code review (median: 6 hours) before deployment. Different engineers write and review the code — here's the data."
Change Failure Rate → Quality Control Evidence
| Regulatory Requirement | What Auditors Want to See | How DORA Data Helps |
|---|---|---|
| Testing before deployment | Changes are validated before production | Low CFR demonstrates effective testing |
| Post-deployment monitoring | Failures are detected and tracked | CFR tracking shows incidents are identified and classified |
| Continuous improvement | Process improves over time | CFR trend shows improvement quarter over quarter |
What to show auditors: "Our Change Failure Rate in Q1 was 8.5%, down from 12% in Q4. Here's the trend chart and the root cause breakdown."
MTTR → Incident Response Evidence
| Regulatory Requirement | What Auditors Want to See | How DORA Data Helps |
|---|---|---|
| Incident response capability | Documented incident response process | MTTR data shows actual response times |
| Timely recovery | Systems are restored within defined SLAs | MTTR demonstrates recovery capability with real data |
| Incident tracking | All incidents are documented with timestamps | MTTR calculation requires and provides this data |
| Business continuity | Organization can recover from disruption | MTTR trend shows recovery capability is maintained |
What to show auditors: "Our median MTTR is 47 minutes. In Q1, we had 21 incidents. The longest recovery took 3.5 hours. Here's the incident log with timestamps for detection, triage, and restoration."
Building an Audit-Ready DORA Dashboard
An audit-ready DORA dashboard differs from an internal engineering dashboard in several ways:
Data Retention
Internal dashboards might show the last 30 days. Audit dashboards need:
- Minimum 12 months of historical data (most regulations require 1–3 years)
- Immutable records (data cannot be retroactively modified)
- Export capability (auditors may request raw data)
Access Control
- Role-based access: Auditors get read-only access
- Audit trail: Log who accessed the dashboard and when
- SSO integration: Use your corporate identity provider (LDAP, SAML)
Content Requirements
Your audit dashboard should show:
Per quarter:
- Deployment Frequency (total count + weekly average)
- Lead Time (median, p75, p95)
- Change Failure Rate (percentage + raw numbers)
- MTTR (median, p75, p95)
- Trend vs. previous quarter
Per deployment:
- Timestamp
- Commit SHA and branch
- Who authored the change
- Who reviewed and approved the change
- CI/CD pipeline status (all stages passed)
- Whether the deployment caused a failure (and if so, recovery details)
Per incident:
- Detection timestamp
- Severity classification
- Affected services
- Root cause category
- Time to restore
- Post-mortem reference
The Compliance Argument for Higher Deployment Frequency
Many fintech CTOs assume regulators want infrequent, heavily-controlled releases. This is a misunderstanding. Regulators want controlled releases. They don't specify frequency.
In fact, the DORA research demonstrates that higher deployment frequency correlates with:
- Lower Change Failure Rate (smaller batches are less risky)
- Lower MTTR (smaller changes are easier to roll back)
- Better audit trails (automated CI/CD captures everything)
- Stronger separation of duties (every change goes through review and automated gates)
The argument to make to auditors and risk committees:
"We deploy 3 times per day instead of once per month. Each deployment is small (median 150 lines of code change), automatically tested by 2,400 tests in our CI pipeline, reviewed by a different engineer, and deployed through an automated pipeline that captures a full audit trail. If any deployment causes an issue, we detect it within 3 minutes and roll back within 10 minutes. Our Change Failure Rate is 8%, and our recovery time is under 1 hour.
Compare this to monthly deployments: 5,000 lines of change, manual testing, higher risk of failure, and a rollback that requires reverting a month of work."
This argument works because regulators care about risk management, not release cadence. Frequent, small, automated deployments with comprehensive audit trails represent better risk management than infrequent, large, partially-manual deployments.
The EU DORA Regulation: Specific Requirements
The EU Digital Operational Resilience Act (the regulation, not the metrics) has specific ICT change management requirements that DORA metrics (the DevOps metrics) directly address:
Article 9: Protection and Prevention
The regulation requires financial entities to implement ICT change management policies that include:
-
Documentation of changes: DORA metrics platforms automatically log every deployment with full metadata.
-
Testing of changes: Lead Time stages show that every change goes through a CI pipeline (testing) before deployment.
-
Risk assessment of changes: Change Failure Rate data provides quantitative risk assessment of the deployment process.
-
Rollback capability: MTTR data demonstrates that the organization can and does roll back failed changes.
-
Post-implementation review: DORA metrics provide automatic post-deployment monitoring through deployment-correlated incident tracking.
Article 11: Response and Recovery
The regulation requires:
-
ICT incident management process: MTTR tracking requires and demonstrates this.
-
Classification of incidents: Change Failure Rate categorization includes incident classification.
-
Timely detection and response: MTTR data shows detection and response times.
Article 25: Testing of ICT Tools and Systems
The regulation requires regular testing of operational resilience. DORA metrics provide ongoing evidence that:
- The deployment pipeline works reliably (Deployment Frequency data)
- Changes are tested (Lead Time stages include CI/CD pipeline data)
- Recovery procedures work (MTTR data from real incidents)
Benchmarks: DORA Performance in Financial Services
Based on the DORA State of DevOps Reports and industry surveys, fintech organizations typically perform as follows:
| Metric | Fintech Median | Fintech Top Quartile | DORA "Elite" |
|---|---|---|---|
| Deployment Frequency | 1–2x per week | Daily | Multiple per day |
| Lead Time | 3–7 days | 1–2 days | Less than 1 hour |
| Change Failure Rate | 10–15% | 5–8% | 0–15% |
| MTTR | 2–6 hours | 30 min–1 hour | Less than 1 hour |
Top-quartile fintech organizations are at or near DORA "Elite" performance. These include major digital banks, payment processors, and trading platforms. This pattern aligns with findings in the Accelerate research (Forsgren, Humble, Kim, 2018): regulation is not a barrier to elite performance — it's an incentive to automate and measure rigorously. The CNCF Annual Survey similarly shows that regulated industries adopting cloud-native practices achieve deployment frequencies comparable to unregulated SaaS companies.
Implementation Guide for Fintech
Phase 1: Instrument (Weeks 1–2)
-
Connect your Git provider to a DORA metrics platform. Ensure the connection captures:
- All merge requests and deployments
- Author and reviewer identity
- Timestamps for all lifecycle events
-
Connect your CI/CD pipeline data. Ensure capture of:
- All pipeline stages and their status
- Build artifacts and their provenance
- Deployment targets (staging, production)
-
Connect your incident tracker. Ensure capture of:
- Incident creation and resolution timestamps
- Severity and impact classification
- Associated deployments (if deployment-caused)
-
Verify data retention meets regulatory requirements (minimum 12 months, ideally 3 years).
Phase 2: Baseline and Context (Weeks 3–4)
- Calculate baseline metrics for the last 90 days.
- Document your deployment process end-to-end, mapping it to DORA stages.
- Create a compliance mapping document showing how each DORA metric addresses specific regulatory requirements.
- Review with your compliance team. Get their input on what additional data auditors might request.
Phase 3: Improve and Document (Months 2–3)
- Set targets for each metric (aligned with DORA "High" performance level as a starting point).
- Run improvement sprints focused on the weakest metric.
- Document all improvements — auditors want to see continuous improvement.
- Create audit-ready reports that can be generated on demand.
Phase 4: Audit Preparation (Ongoing)
- Prepare a DORA metrics briefing for auditors. Explain what each metric measures and how it relates to their requirements.
- Maintain a FAQ based on previous auditor questions.
- Run quarterly internal audits of your DORA data accuracy (are all deployments captured? Are incidents correctly classified?).
- Keep historical data accessible and exportable.
Enterprise Client Requirements
Beyond regulators, enterprise fintech clients often require evidence of engineering maturity during vendor due diligence. DORA metrics address common RFP questions:
| RFP Question | DORA Answer |
|---|---|
| "What is your release cadence?" | Deployment Frequency data with trend |
| "How do you manage change control?" | Lead Time stages showing review, testing, and approval |
| "What is your production failure rate?" | Change Failure Rate with quarterly trend |
| "How quickly do you recover from incidents?" | MTTR with percentile breakdown |
| "Do you have automated testing?" | CI/CD pipeline data within Lead Time metrics |
| "What is your rollback procedure?" | MTTR data showing actual rollback execution times |
| "How do you ensure separation of duties?" | Lead Time stages showing different participants for authoring, reviewing, and deploying |
Having DORA data ready for these questions differentiates you from competitors who can only provide policy documents. Data beats documentation.
Security and Deployment Considerations
Fintech organizations often have stricter security requirements for any tool that accesses their codebase. Key considerations when choosing a DORA metrics platform:
On-premise deployment: Some organizations cannot send code metadata to cloud services. PanDev Metrics offers on-premise deployment, keeping all data within your infrastructure.
SSO/LDAP integration: Access control must integrate with your identity provider. PanDev Metrics supports LDAP and SSO.
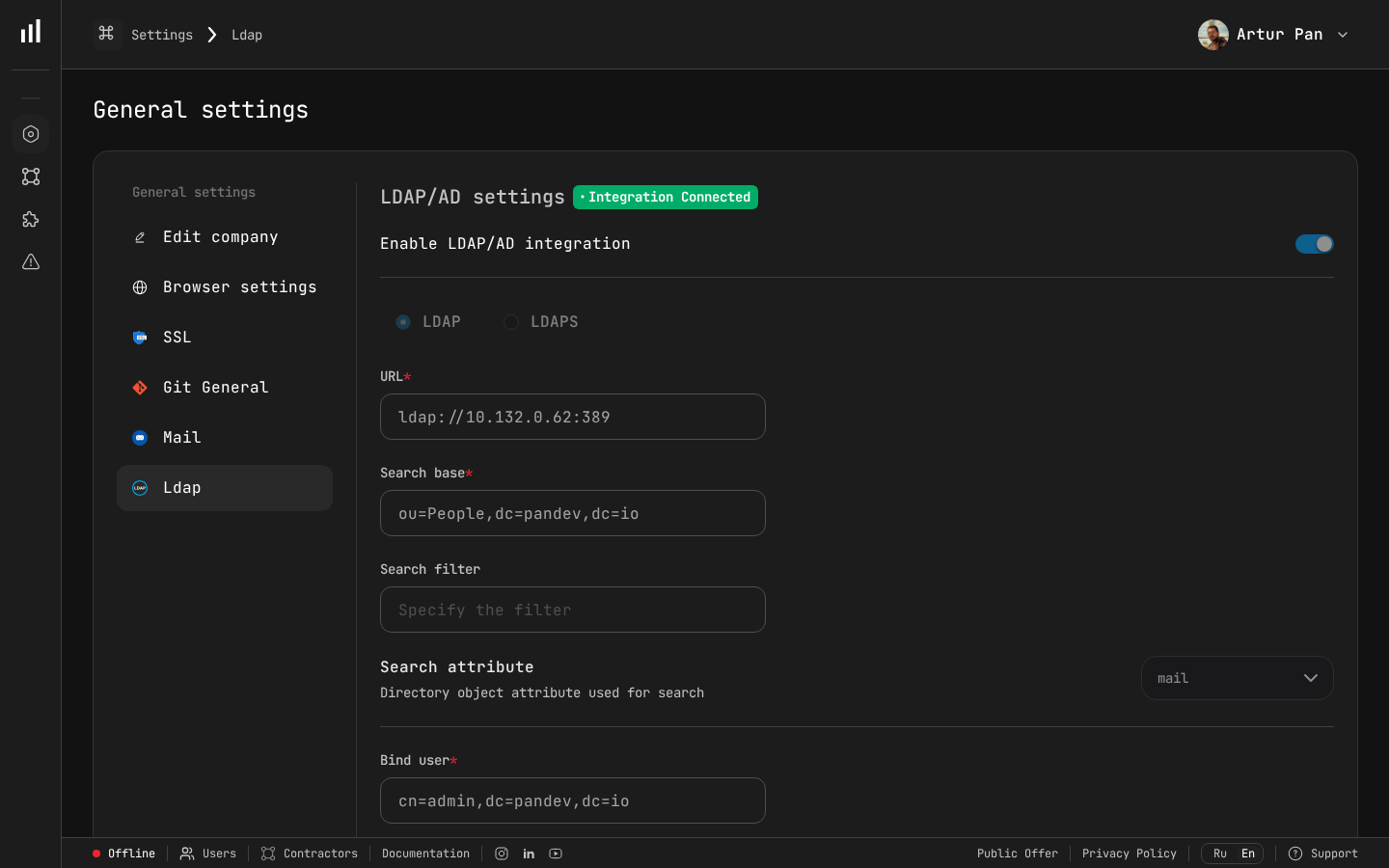
LDAP/AD integration settings with enterprise security compliance.
Data classification: DORA metrics platforms access commit messages, branch names, and MR titles — which may contain references to security issues or customer data. Ensure your platform encrypts data at rest and in transit, and that access is audited.
Network security: The platform should only require outbound connections to your Git provider API. No inbound ports, no agent installation on production servers, no access to source code contents (only metadata).
Real-World Compliance Scenarios
Scenario 1: SOC 2 Audit
Auditor question: "Show me evidence that all production changes go through your change management process."
Traditional answer: Policy document + sample of 25 change records manually compiled.
DORA-powered answer: Live dashboard showing 100% of 847 production deployments in the audit period, each with automated CI/CD pipeline records, code review approvals, and deployment timestamps. Exportable as CSV.
Scenario 2: EU DORA Regulation Compliance Review
Regulator question: "Demonstrate your ICT change management and incident response capabilities."
Traditional answer: 30-page policy document + quarterly test results.
DORA-powered answer: 12-month DORA metrics dashboard showing:
- 1,247 deployments with full audit trail
- Median Lead Time of 2.8 days with stage breakdown
- Change Failure Rate of 7.2% (below industry median)
- Median MTTR of 38 minutes with incident classification
- Quarter-over-quarter improvement trend
Scenario 3: Enterprise Client Due Diligence
Client question: "How mature is your engineering process? We need confidence that your platform will be reliable."
Traditional answer: Architecture diagram + SLA commitment.
DORA-powered answer: "We deploy to production 4x per day. Our median Lead Time is 1.8 days. Our Change Failure Rate is 6%. When failures occur, we recover in under 45 minutes on average. Here's our DORA dashboard showing the last 12 months of data. We benchmark as 'Elite' on 3 of 4 metrics and 'High' on the fourth."
The Competitive Advantage
Fintech companies that track DORA metrics gain three competitive advantages:
-
Faster audits. Instead of weeks of document preparation, generate reports on demand. Auditors spend less time requesting evidence and more time on substantive review.
-
Stronger sales. Enterprise clients choose vendors with demonstrable engineering maturity. DORA data is more convincing than marketing claims.
-
Better engineering. The metrics don't just satisfy auditors — they actually improve your delivery process. You ship faster, break less, and recover quicker.
In a market where every fintech claims "bank-grade security" and "enterprise reliability," DORA metrics provide proof. As the Basel III operational risk framework evolves to cover ICT risk more explicitly, having quantitative engineering data will shift from competitive advantage to regulatory necessity.
Benchmarks from the DORA State of DevOps Reports (2019–2023), published by Google Cloud / DORA team. Regulatory references: EU Regulation 2022/2554 (Digital Operational Resilience Act), PCI DSS v4.0, SOC 2 Trust Services Criteria.
Need audit-ready DORA metrics for your fintech? PanDev Metrics provides automated DORA tracking with on-premise deployment, LDAP/SSO, and full data export — built for regulated environments. See how it works →
