Engineering Metrics in Fintech: Compliance, Speed, and Security
Fintech CTOs live in a unique pressure cooker: regulators demand audit trails and compliance evidence, the business demands rapid feature delivery, and security teams demand zero vulnerabilities. These three forces constantly pull engineering organizations in different directions.
The good news? Engineering metrics can help you satisfy all three — without turning your team into a bureaucratic machine. Research from the DORA State of DevOps Reports consistently shows that elite performers don't trade speed for stability — they achieve both simultaneously.
{/* truncate */}
The Fintech Engineering Trilemma
Every fintech CTO faces the same impossible triangle:
- Compliance — PCI DSS 4.0, SOC 2 Type II, PSD2, GDPR, and the EU's Digital Operational Resilience Act (DORA Regulation) require documented processes, audit trails, and provable controls
- Speed — Competitors ship features weekly; your customers expect the same. The Bessemer Cloud Index shows top fintech companies deploy multiple times per day.
- Security — A single breach can cost millions in fines and destroy customer trust overnight. The EBA Guidelines on ICT and Security Risk Management make security posture a board-level concern.
Traditional management treats these as trade-offs. You can have two, but not all three. Engineering metrics change this equation by making all three dimensions visible and measurable simultaneously.
Why Traditional Project Management Fails in Fintech
Most fintech companies start with Jira boards and sprint velocity. These tools tell you what the team planned to do and whether tickets moved across columns. They don't tell you:
- How long code actually sits in review waiting for a compliance-mandated second approval
- Whether security fixes are being prioritized or perpetually pushed to the next sprint
- How much developer time is spent on compliance-related work versus feature development
- Whether your change failure rate is trending up as you accelerate delivery
Without this visibility, CTOs make decisions based on gut feeling and team leads' subjective reports. In a regulated industry, that's not just inefficient — it's risky.
The Five Metrics That Matter for Fintech
1. Deployment Frequency With Change Categorization
Standard DORA metrics track how often you deploy. In fintech, what you deploy matters as much as how often. You need to categorize deployments:
- Feature releases — new customer-facing functionality
- Compliance updates — changes mandated by regulatory requirements
- Security patches — vulnerability fixes and dependency updates
- Infrastructure changes — platform and tooling updates
When you can see deployment frequency broken down by category, patterns emerge. If compliance updates are consuming 40% of your deployment pipeline, that's a signal to invest in automation. If security patches are infrequent, that might indicate a backlog of unaddressed vulnerabilities.
PanDev Metrics tracks deployment frequency across your GitLab, GitHub, Bitbucket, or Azure DevOps pipelines, giving you this breakdown without manual categorization overhead.
2. Lead Time for Changes — With Compliance Gates
In most industries, lead time for changes measures the time from first commit to production deployment. In fintech, the pipeline includes mandatory gates:
- Code review (often requiring two approvals for payment-related code)
- Security scanning
- Compliance review for regulated features
- Staging environment testing with synthetic data
Measuring the total lead time isn't enough. You need to see where time is spent at each gate. If code review takes 2 hours but compliance review takes 3 days, you know exactly where to focus improvement efforts.
With PanDev Metrics, you can track each stage of your pipeline and identify bottlenecks that slow delivery without adding risk.
3. Change Failure Rate by Service Criticality
Not all failures are equal. A bug in your marketing landing page is different from a bug in your payment processing engine. Fintech CTOs need change failure rate segmented by service criticality:
- Tier 1 (Critical) — Payment processing, transaction engines, authentication systems
- Tier 2 (Important) — Customer dashboards, reporting systems, internal tools
- Tier 3 (Standard) — Marketing pages, documentation, non-customer-facing services
A 5% change failure rate across the board might seem acceptable. But if your Tier 1 services have a 10% failure rate while Tier 3 services have 1%, you have a serious problem hiding behind an average.
4. Developer Activity Distribution
Understanding how your engineering team's time is distributed across different types of work is critical in fintech. IDE heartbeat tracking and activity monitoring reveal the actual split between:
- Feature development — building new capabilities
- Compliance work — implementing regulatory requirements, documentation
- Security remediation — fixing vulnerabilities, updating dependencies
- Maintenance — bug fixes, technical debt reduction
- Code review — reviewing others' work (often higher in fintech due to mandatory reviews)
PanDev Metrics' IDE heartbeat tracking captures this data automatically from 10+ supported IDEs, showing you Focus Time and Activity Time broken down by project and repository.
5. Mean Time to Recovery (MTTR)
In fintech, downtime isn't just lost revenue — it can trigger regulatory reporting requirements. Under PSD2, payment service providers must report major operational incidents to their national authority. The Basel III operational risk framework further quantifies downtime as a capital-impacting event.
Tracking MTTR by service tier helps you:
- Prove to regulators that you have effective incident response
- Identify services that need better monitoring or redundancy
- Justify investment in reliability engineering
Building Your Compliance Evidence Trail
Regulators don't just want you to be compliant — they want you to prove it. Engineering metrics create an automatic evidence trail:
For SOC 2 audits:
- Deployment logs showing consistent change management processes
- Code review metrics proving mandatory review policies are followed
- Lead time data demonstrating controlled, non-rushed releases
For PCI DSS compliance:
- Change failure rates showing payment systems are thoroughly tested
- Activity logs demonstrating separation of duties
- Recovery time metrics proving incident response capability
For regulatory reporting:
- Uptime and availability data from deployment and recovery metrics
- Evidence of security patch deployment timelines
- Documentation of development process controls
PanDev Metrics supports on-premise deployment, which is often a requirement for fintech companies handling sensitive financial data. Your metrics data stays within your infrastructure, behind your firewall.
Practical Implementation: A Phased Approach
Phase 1: Foundation (Weeks 1-2)
Start with the basics:
- Connect your Git platform (GitLab, GitHub, Bitbucket, or Azure DevOps) to PanDev Metrics
- Deploy IDE plugins to your development team (supports VS Code, JetBrains IDEs, Vim, and more)
- Establish baseline measurements for DORA metrics
Don't try to change anything yet. Just observe.
Phase 2: Visibility (Weeks 3-4)
Share dashboards with team leads:
- Show deployment frequency trends
- Highlight lead time bottlenecks (compliance gates will likely stand out)
- Present change failure rates by service
Let the team react to the data. Often, just making metrics visible drives improvement without any top-down mandates.
Phase 3: Optimization (Month 2+)
Now you have enough data to make informed decisions:
- Automate compliance gates that cause the biggest delays
- Invest in testing for services with high change failure rates
- Rebalance team allocation if compliance work is crowding out feature development
- Set targets based on your own baselines, not industry benchmarks
Phase 4: Continuous Evidence (Ongoing)
Use metrics dashboards as living compliance documentation:
- Export reports for audit preparation
- Set alerts for anomalies (sudden spike in change failure rate, drop in deployment frequency)
- Review trends quarterly with leadership and compliance teams
Common Pitfalls to Avoid
Don't use metrics as individual performance measures. Fintech developers already deal with extra review requirements and compliance overhead. Using activity tracking to judge individuals will destroy trust and morale. Focus on team-level and system-level metrics.
Don't set targets before you have baselines. Every fintech organization is different. A company processing millions of transactions daily has different constraints than one building a B2B lending platform. Measure first, then set realistic improvement targets.
Don't ignore the compliance cost. If your metrics show that 30% of engineering time goes to compliance-related work, that's not a problem to fix — it's a reality to plan around. Use this data for capacity planning and roadmap discussions with the business.
Don't deploy metrics without team buy-in. Explain to your team why you're tracking these metrics. In fintech, the answer is straightforward: regulators require evidence of controlled processes, and metrics automate that evidence collection.
The ROI of Engineering Metrics in Fintech
The return on investment for engineering intelligence in fintech comes from three sources:
-
Reduced audit preparation time. Companies using engineering metrics report spending ~40-60% less time preparing for SOC 2 and PCI DSS audits because evidence is continuously collected rather than manually assembled.
-
Faster identification of bottlenecks. When you can see that compliance review is your biggest lead time contributor, you can invest in automation (policy-as-code, automated compliance checks) rather than guessing.
-
Better resource allocation. Understanding the actual split between feature work, compliance, and security helps you staff teams appropriately and set realistic delivery expectations with the business.
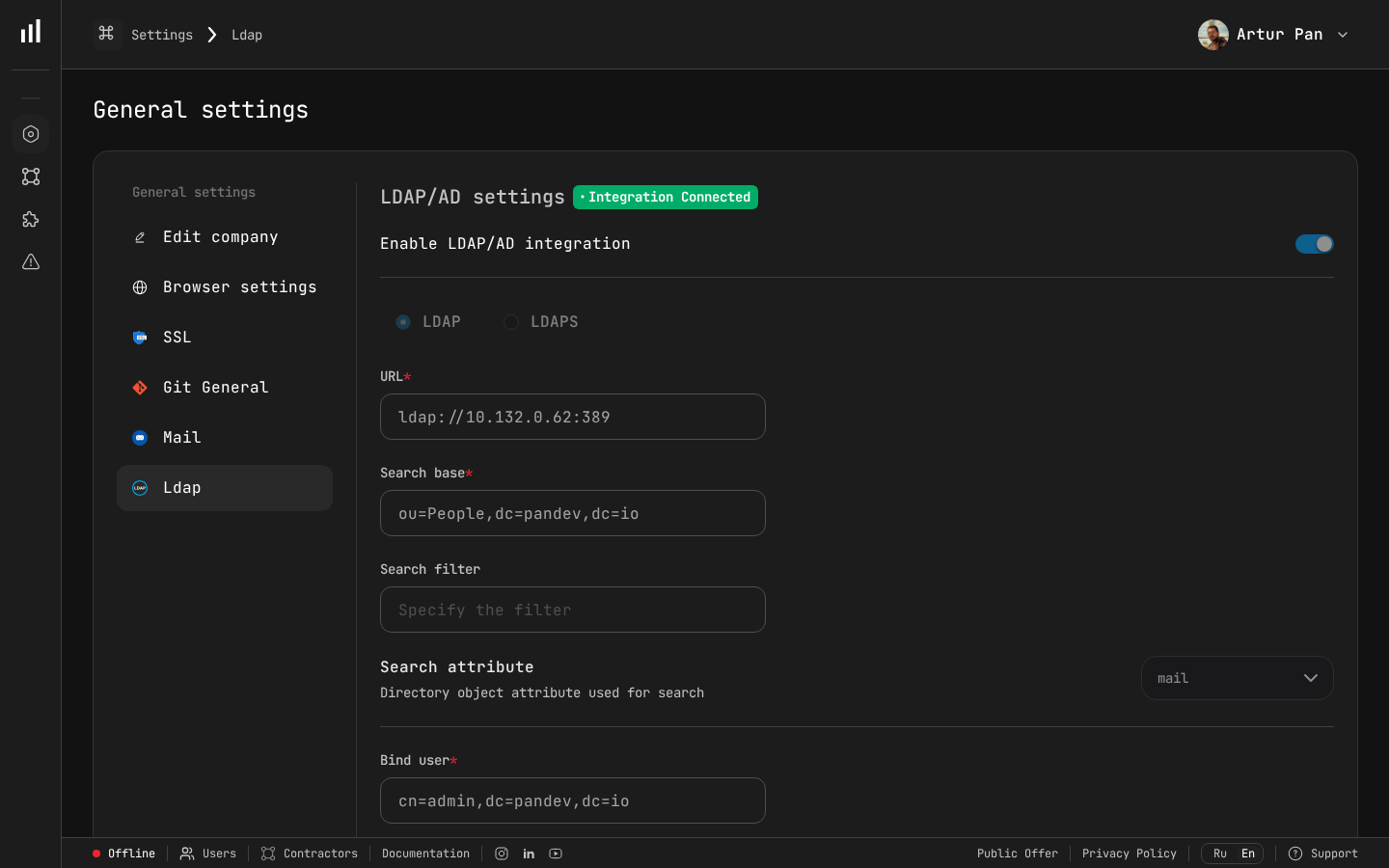 LDAP/Active Directory integration ensures PanDev fits into your existing enterprise authentication infrastructure — a common requirement in fintech environments.
LDAP/Active Directory integration ensures PanDev fits into your existing enterprise authentication infrastructure — a common requirement in fintech environments.
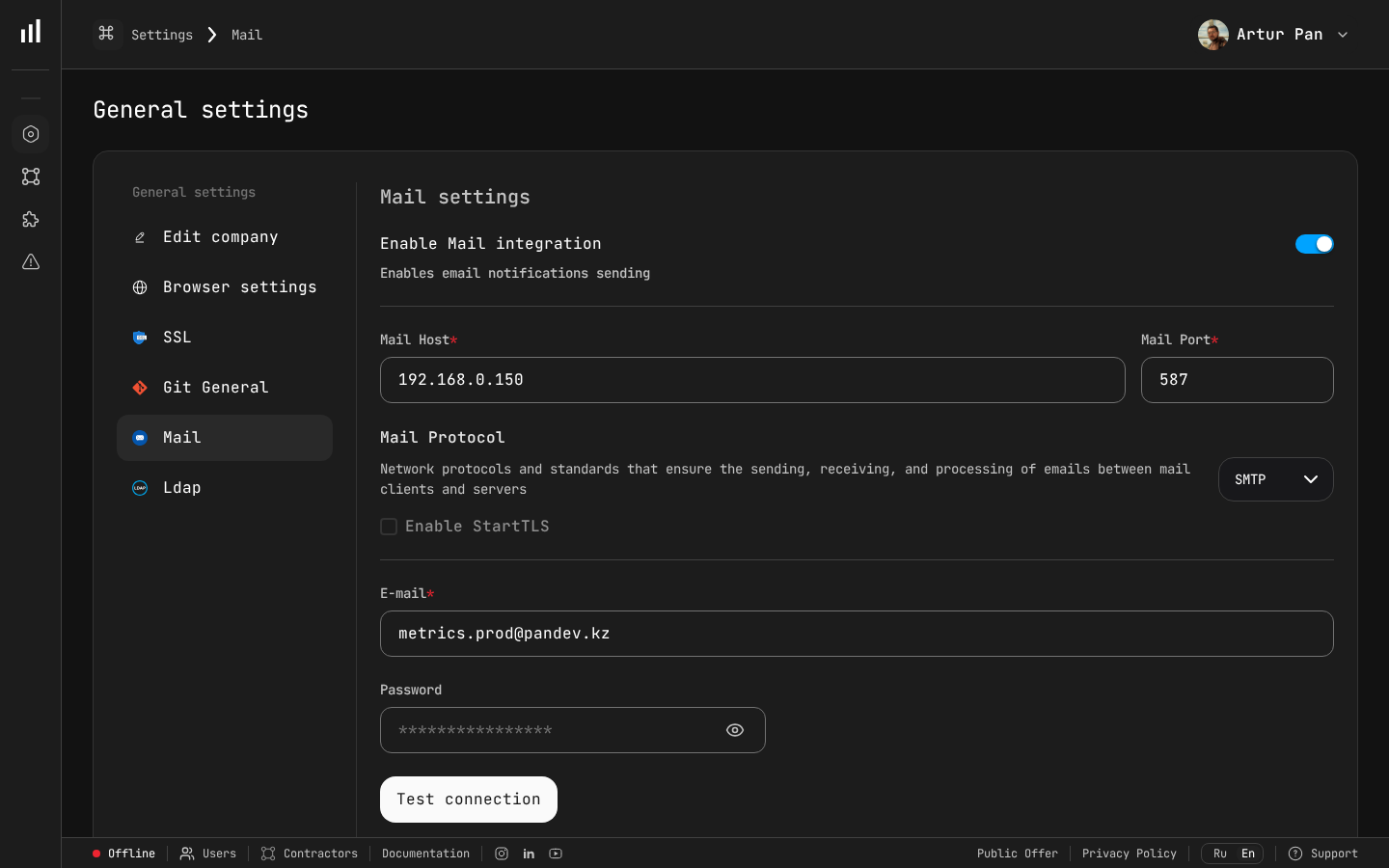 Enterprise mail configuration ensures notifications and alerts route through your organization's internal SMTP server — keeping all communication within your network perimeter.
Enterprise mail configuration ensures notifications and alerts route through your organization's internal SMTP server — keeping all communication within your network perimeter.
Security and Data Privacy Considerations
Fintech companies rightfully worry about adding any new tool to their stack. Key considerations:
- On-premise deployment — PanDev Metrics can be deployed entirely within your infrastructure, ensuring engineering data never leaves your network
- LDAP/SSO integration — fits into your existing authentication infrastructure
- Multi-tenancy — if you have multiple teams or business units, each can have isolated data
- Data minimization — activity tracking captures patterns, not code content
Conclusion
Fintech engineering doesn't have to be a choice between compliance, speed, and security. With the right metrics infrastructure, these three dimensions become complementary rather than competing.
Start by measuring what's actually happening. Then use that data to remove bottlenecks, automate compliance evidence, and build the kind of engineering organization that regulators trust and customers love.
Ready to bring engineering intelligence to your fintech team? PanDev Metrics — on-premise deployment, DORA metrics, IDE activity tracking, and compliance-ready reporting for regulated industries.
